The Research Connection – December 2019: Software Edition

Featured R&D projects:
- AiMOS – Artificial Intelligence Multiprocessing Optimized System
- A Self-Protecting 5G System Using Quantum Computing Approaches
- Improving Deepfake Detection
- Expanding Wireless Technology
- Where’s Waldo? Identifying Cyberattacks using Low-Level Hardware Information
This edition’s contributors: SUNY Research Foundation | SUNY Polytechnic Institute | University at Albany | Clarkson University | Rensselaer Polytechnic Institute
AiMOS – Artificial Intelligence Multiprocessing Optimized System
 Description: The most powerful supercomputer to be housed at a private university was recently installed at the Rensselaer Polytechnic Institute Center for Computational Innovations. Part of a collaboration between IBM, Empire State Development (ESD), NY CREATES and Rensselaer, the 8 petaflop AI supercomputer is uniquely configured to enable AI calculations to reach their full potential. Potential public and private industry partners interested in learning more about AiMOS should contact CCI Director Christopher Carothers.
Description: The most powerful supercomputer to be housed at a private university was recently installed at the Rensselaer Polytechnic Institute Center for Computational Innovations. Part of a collaboration between IBM, Empire State Development (ESD), NY CREATES and Rensselaer, the 8 petaflop AI supercomputer is uniquely configured to enable AI calculations to reach their full potential. Potential public and private industry partners interested in learning more about AiMOS should contact CCI Director Christopher Carothers.
Potential applications: AI research, computation, modeling, machine learning, deep learning, simulations
Contact info: Christopher Carothers, Director, CCI, carotc@rpi.edu
A Self-Protecting 5G System Using Quantum Computing Approaches
 Description: As the world prepares for the debut of 5G wireless, researchers at SUNY Polytechnic Institute are reimagining network security. The project integrates an Autonomous Security Management Framework (ASMF) with Quantum Information Science (QIS) to allow 5G systems to identify, assess, and respond to attacks without human intervention. Contact us today to collaborate with the research team.
Description: As the world prepares for the debut of 5G wireless, researchers at SUNY Polytechnic Institute are reimagining network security. The project integrates an Autonomous Security Management Framework (ASMF) with Quantum Information Science (QIS) to allow 5G systems to identify, assess, and respond to attacks without human intervention. Contact us today to collaborate with the research team.
Potential applications: Next-generation 5G cellular systems, cloud-based networks, and quantum computing approaches.
Contact: Dr. Hisham Kholidy, Assistant Professor, Network and Computer Security Department, kholidh@sunypoly.edu
Improving Deepfake Detection
 Description: University at Albany Professor of Computer Science Siwei Lyu is at the forefront of deepfake detection. He has developed algorithms that have helped expose fake videos by tracking the differences in eye movement of bogus content when compared with legitimate sources. His research team is partnering with Facebook, Microsoft and the Partnership on AI to develop better open source tools to detect deepfakes. Support this research, collaborate with the research team.
Description: University at Albany Professor of Computer Science Siwei Lyu is at the forefront of deepfake detection. He has developed algorithms that have helped expose fake videos by tracking the differences in eye movement of bogus content when compared with legitimate sources. His research team is partnering with Facebook, Microsoft and the Partnership on AI to develop better open source tools to detect deepfakes. Support this research, collaborate with the research team.
Potential applications: These techniques can be used to detect online deepfake videos and protect users from malicious disinformation involving deepfakes.
Contact: Siwei Lyu, Professor, Computer Science, slyu@albany.edu
Expanding Wireless Technology
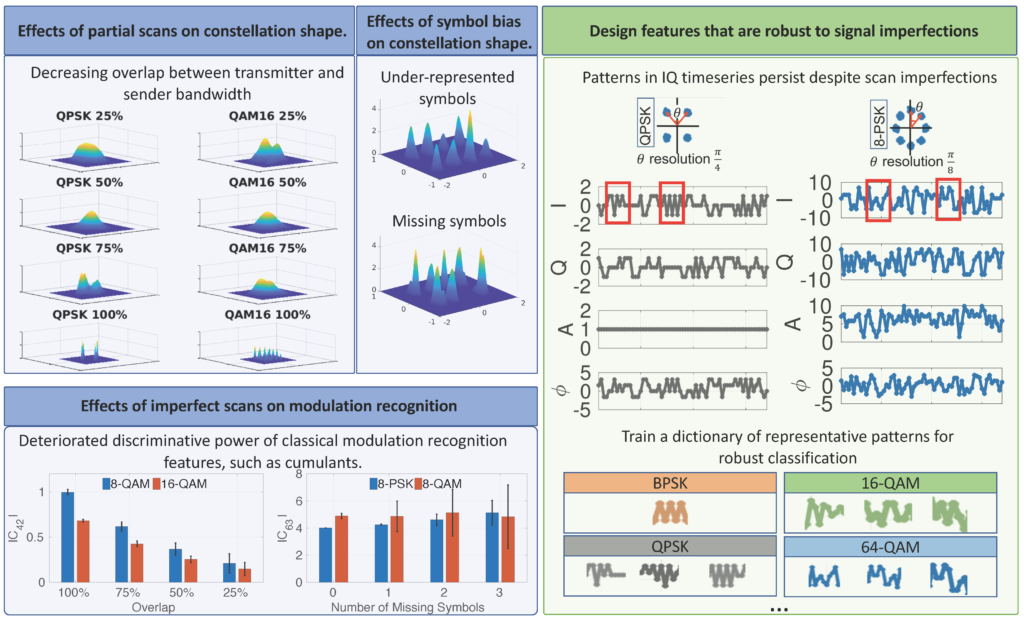 Description: The radio spectrum is instantly renewable. As soon as one device is done using it, another device can jump right on. To use this resource more effectively, University at Albany computer scientist Mariya Zheleva is designing new signal features and algorithms to help wireless devices to make smarter decisions when selecting when and where in the spectrum to operate. This project is part of Zheleva’s continuing efforts to improve spectrum-sharing networks in infrastructure-challenged environments. These projects hold the potential to improve emergency preparedness and response, agriculture, healthcare, and environmental monitoring. Collaborate with the research team. Contact us today.
Description: The radio spectrum is instantly renewable. As soon as one device is done using it, another device can jump right on. To use this resource more effectively, University at Albany computer scientist Mariya Zheleva is designing new signal features and algorithms to help wireless devices to make smarter decisions when selecting when and where in the spectrum to operate. This project is part of Zheleva’s continuing efforts to improve spectrum-sharing networks in infrastructure-challenged environments. These projects hold the potential to improve emergency preparedness and response, agriculture, healthcare, and environmental monitoring. Collaborate with the research team. Contact us today.
Potential applications: Wireless networks, deployment and monitoring, cognitive radio and dynamic spectrum access, networking for developing regions.
Contact: Dr. Mariya Zheleva, Assistant Professor of Computer Science, mzheleva@albany.edu
Where’s Waldo? Identifying Cyberattacks using Low-Level Hardware Information
 Description: Research by the Computer Architecture and Microprocessor Engineering Lab at Clarkson University focuses on a novel defending mechanism against cyberattacks, especially malware. The mechanism monitors the regular execution of software and detects malware attacks via anomaly detection through a software-hardware integrated, data-driven, machine learning supported approach. The long-term goal is to enhance the mechanism to the point where it can be widely adopted as an effective method to improve the security of computing systems.
Description: Research by the Computer Architecture and Microprocessor Engineering Lab at Clarkson University focuses on a novel defending mechanism against cyberattacks, especially malware. The mechanism monitors the regular execution of software and detects malware attacks via anomaly detection through a software-hardware integrated, data-driven, machine learning supported approach. The long-term goal is to enhance the mechanism to the point where it can be widely adopted as an effective method to improve the security of computing systems.
Contact: Chen Liu, Department of Electrical and Computer Engineering, cliu@clarkson.edu
Potential Application: Cybersecurity.
About The Research Connection: The Research Connection is a quarterly feature in the Center for Economic Growth’s monthly, online newsletter, The CEG Indicator. This special feature highlights R&D being conducted by researchers at Capital Region colleges and universities and others throughout the SUNY system. The Research Connection spotlights academic R&D in CEG’s focus technology sectors: Nanotechnology and Semiconductors, Cleantech/Energy, Biotechnology, Advanced Materials, Population Health Technology and Information Technology.
Each edition of The Research Connection will highlight several research projects in a specific technology sector. The Research Connection will keep CEG investors (2,500+) and CEG Indicator subscribers (9,000+) informed on the cutting-edge R&D that is being conducted by SUNY and other academic researchers that could potentially transform their industries. It will also encourage collaboration, patent, licensing and other opportunities.
Don’t miss these insights into the trends that are shaping the Capital Region’s economy. Sign up for CEG’s e-news and follow us on: